
Cybersecurity Audit Singapore: Your Questions Answered
How sure are you that your business can face today’s digital dangers? Many think basic security is enough. But data breaches and compliance violations still hit businesses of all sizes.
SeqOps is your trusted partner in building a secure, reliable, and compliant infrastructure. Through our advanced platform and methodical approach, we ensure your systems remain protected against vulnerabilities while staying ready to handle any challenge.

How sure are you that your business can face today’s digital dangers? Many think basic security is enough. But data breaches and compliance violations still hit businesses of all sizes.

When was the last time you checked your digital defenses against the billion cyberattacks blocked monthly worldwide? If you’re unsure, you’re not alone. But ignoring this could cost your business

Is your organization ready to face today’s advanced cyber threats? Many think their IT is secure, but vulnerabilities often hide until a detailed check finds them. An information security examination

Could your organization survive a $4.88 million financial hit from a security breach? This figure shows the average cost businesses faced in 2024. It’s why knowing about Information Security Assessment

Are you sure your company’s systems can fight off today’s cyber threats? Many business leaders aren’t sure, and the risks are huge. Recent studies show a scary fact: 98% of

When was the last time you truly verified your organization’s security measures? This is the core of every Business Security Audit. It checks if your controls really protect against threats.

The digital world has turned into a battlefield. Cybercrime costs hit $9.4 million worldwide in 2024. Every business is under attack by skilled hackers looking to find weak spots. Information

Is your organization ready for the 1,636 cyberattacks it faces every week? In today’s world, this is not just a worry—it’s a real threat that needs urgent action. The cost

When did you last check your apps for hidden dangers that could harm your business? Statistics are alarming. Research shows that 83% of applications contain one or more vulnerabilities when

How sure are you that your company can handle the next cyber threat? With cybercrime costs expected to hit $10.5 trillion annually by 2025, leaders are worried. They need to

Could your organization withstand a sophisticated cyber attack tomorrow? This question keeps business leaders awake at night, and for good reason. Recent data reveals a sobering reality: 15,009,813 data records
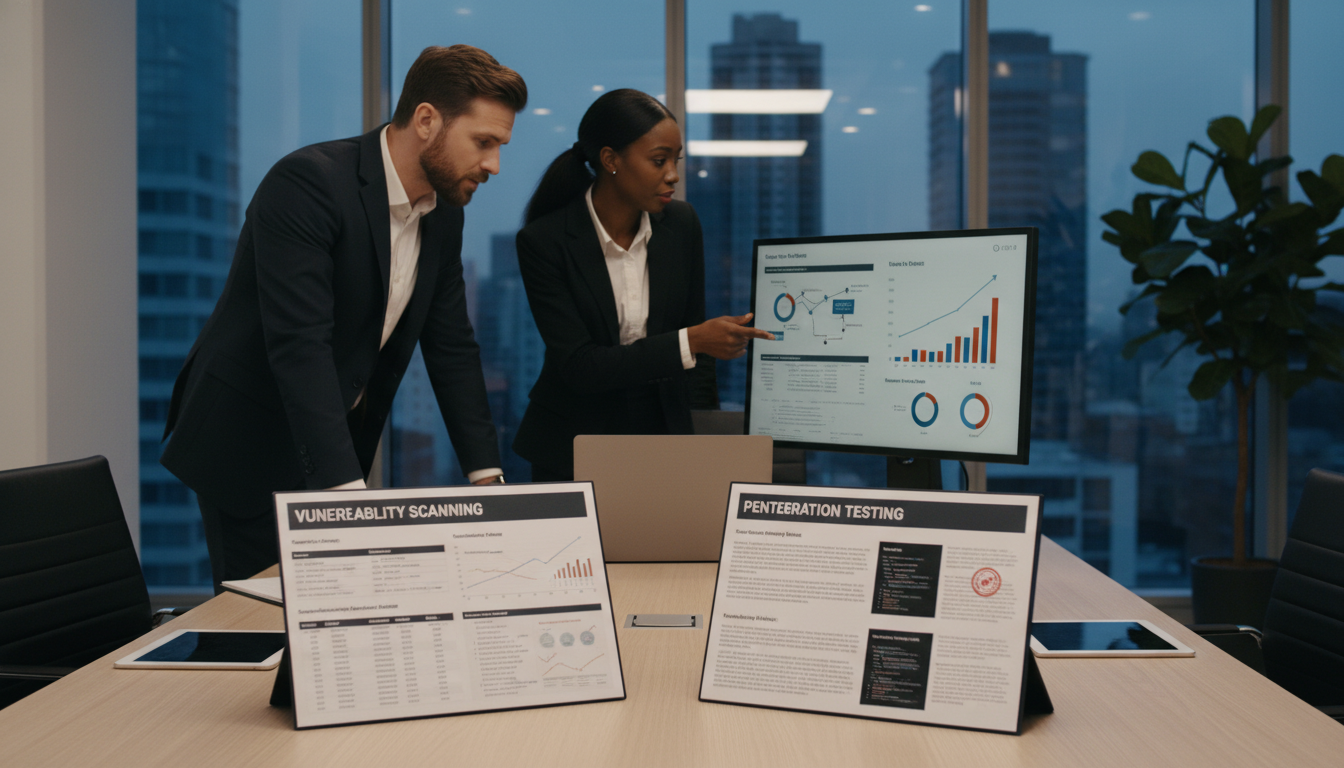
Are you using the right cybersecurity methods to protect your digital assets? Many leaders struggle to pick the best security approach. This can leave their systems open to threats. There

A staggering 60% of small companies go out of business within six months of a significant cyberattack. This statistic highlights a harsh reality for modern enterprises. Your digital infrastructure is
In 2023, the FBI’s Internet Crime Complaint Center received a staggering 880,418 cyber complaints. This represents a 10% increase from the previous year, with potential losses exceeding $12.5 billion. This
A staggering 80% of security breaches now target the software that powers modern business. This fact underscores a critical reality. Your digital operations face constant, sophisticated threats. We recognize that
A recent analysis revealed that over 30% of all active websites rely on a single, foundational web server technology. This staggering figure highlights a massive, interconnected ecosystem where a single

A staggering 60% of data breaches originate from security gaps in internet-facing infrastructure. This fact highlights a critical reality for modern organizations. Protecting your business demands a proactive stance against

Many business leaders believe they are fully protected because they run regular security scans. This common misconception can leave critical gaps in your defenses. We often see organizations investing in

Can a single review reshape how your business defends its most valuable data? We conduct a comprehensive digital security audit to validate controls, reduce risk, and show compliance. This review

What if a single, well-crafted review could change how your company resists threats and proves compliance? We introduce our comprehensive internal security audit program designed for U.S. organizations that need
Can a single, well-run audit truly cut risk and prove your controls work for customers and regulators? We open with that question because leaders must decide where to invest time
Can your digital front door withstand today’s clever attacks, or is risk quietly growing behind the scenes? We partner with teams to run a focused security audit that checks core
How confident are you that a single lapse won’t expose your company to a major breach? That question guides our approach. We combine modern tools and proven processes to give
How confident are you that your online operations truly resist today’s threats? We provide website security audit services that validate controls, policies, and configurations against recognized frameworks. Our approach blends

Can a single, structured review stop a breach before it costs millions and damages trust? We open with that question because the numbers are stark: global cyberattack costs may top
Are your defenses really keeping pace with today’s threats? Every week, organizations face over 1,636 cyberattacks, and the average cost of a breach hit $4.88 million in 2024. We present

Could a single structured assessment reveal hidden gaps that put your company at risk? We ask this because recent reports show cyber and data threats top the list of concerns
Can one structured review stop a breach before it costs millions? Cyber threats rose 46% year over year, and public-cloud breaches now average $5.17 million. These figures show why proactive

Can a single, well-run review truly transform how your organization resists cyber threats? We ask this because we believe audits should do more than check boxes. A structured review verifies

Can a single, structured review stop cascading failures across critical systems before costs spiral? We believe a focused review keeps teams ahead of threats and protects business continuity. Our guide

Can you afford to wait until a breach shows up in your logs? The cost of inaction is rising: the average data breach now costs $4.45 million, and recorded CVEs
How secure is your organization when remote work widens the attack surface and cybercrime costs skyrocket? We outline a practical view of a security audit and show how it evaluates
What if a routine check could reveal hidden gaps that leave your network exposed? We partner with organizations to deliver a focused, repeatable review that aligns controls with evolving network
How confident are you that your company could withstand the next costly breach? We write as partners who translate technical findings into business priorities. Our guide shows how a rigorous
How well can your organization withstand the 1,636 cyberattacks it faces every week? We ask this because the average cost of a data breach reached $4.88 million in 2024, and

Can you afford to assume your defenses are enough? We ask this because many businesses only discover gaps after an incident. We help teams find and fix those gaps before

Can a single independent review reveal hidden gaps that threaten your business resilience? We start with a clear goal: align controls to recognized frameworks so your company protects critical information
How confident are you that your controls will hold up under real-world pressure? We help businesses move beyond checklist reviews and deliver a defensible, business-aligned program that unifies governance, risk,
Can we really stop the next costly breach before it reaches our balance sheet? That question frames every decision we make as leaders. We present a practical blueprint that helps
How confident are you that your infrastructure can withstand the next wave of digital threats? We help leaders answer that question with a clear, business-focused network security audit. Our approach
Can a single review truly reveal the gaps that put your business at risk? We open with this question because clarity matters before action. We perform a systematic review of

Question: Are you sure your organization can prove continuous protection and compliance across complex environments? We define a cloud security audit as a repeatable evaluation of accounts, configurations, identities, networks,